Every desktop on the web is allotted a distinctive address, which is known as IP address. A normal IP-address seems like this: 199.123.456.7. It’s quite hard to remember the IP-address of all the sites we visit regularly. Instead words are easy to keep in mind compared to the numbers. That’s where domains come into picture. When you go to the site, you will just require knowing a domain name. Computers memorize numbers, and domain name system aids us change the domain-name into an IP-address that the system can recognize. When you enter domain.com to your web browser, then your browser initially require getting the IP-address of www.domain.com. The web browser communicates a domain-name-system to inquiry the server location where the pages are saved. Visualize it as an IP address’s directory-service.
However, it’s obvious to a PC as they don’t understand language. In its place, they speak in numbers. Rather than domains, the web and other networks make use of IP (internet protocol) addresses that are written in numerals. It’s in converting the human-name for a website to the system name for the website that domain name system comes into view. Many people explains DNS as the “phone-directory” of the web however we consider it as a traditional phone operator or switchboard.
How DNS works?
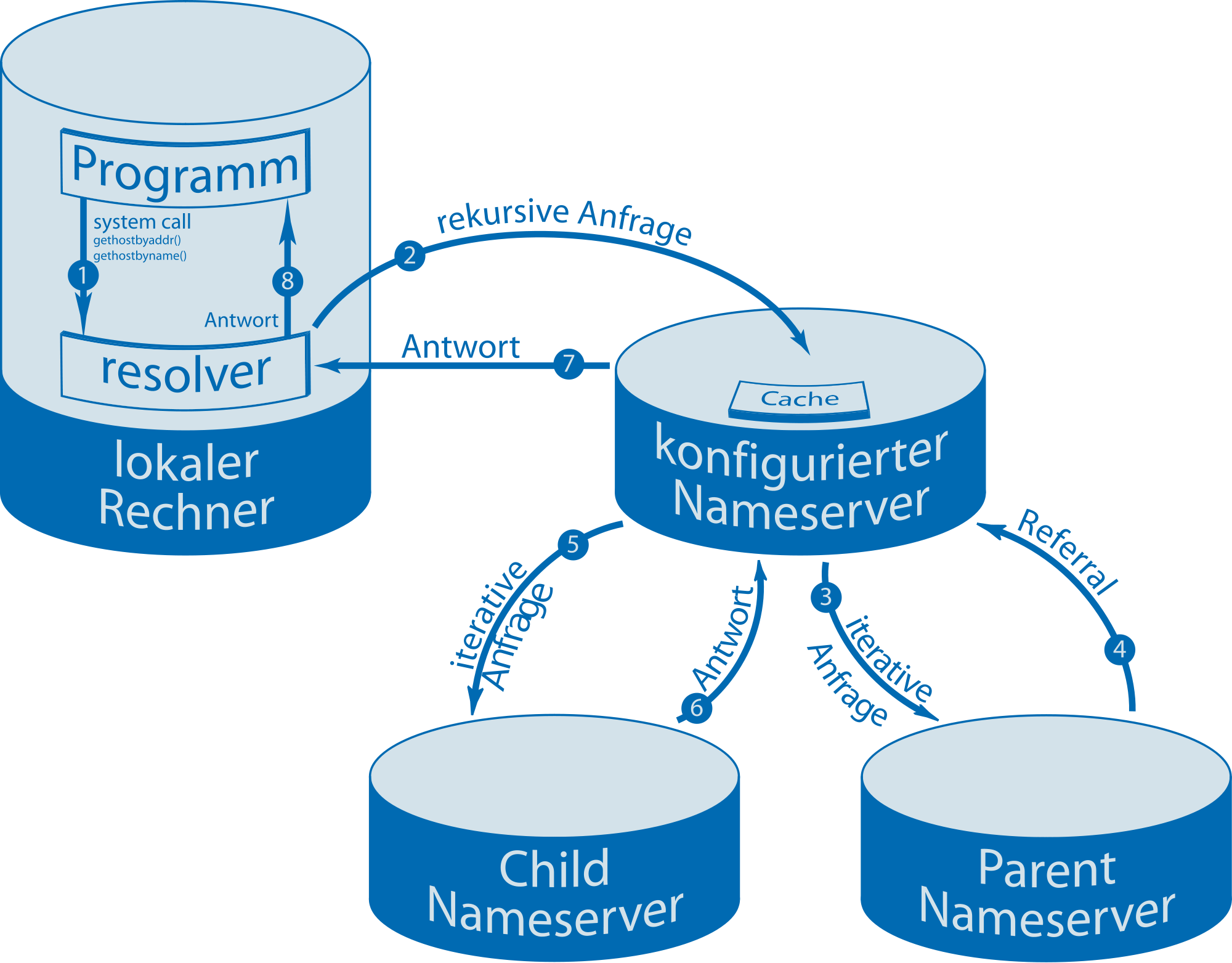
Whenever you enter a web address (such as facebook.com) into your web browser, then your tablet or phone or computer figure out what IP address (number) is related with that domain. Then it links to that IP-address and redirects you to the official website of facebook.com. After that your PC will save that IP address so that another time, it does not have to reach the domain-name-system and can simply access Google directly. But, after some time – of when you delete your cache due to some reason – your PC system is about to remove that IP-address, which implies it has to again reach out.
The problem takes place when robbers attack your PC with malware and indicate it to a false DNS server having the IP addresses which act and look like the website you are attempting to access however really are not that website at all. For instance, accessing your internet banking, from one of these DNS is similar to walking into your brick-and-mortar bank within your city, providing the clerk all your required details, and then knowing that it’s really your bank’s hologram and all your cash has just been taken by clever robbers from the future.
So what are the ways to protect yourself? Clearly you are not about to stop accessing internet banking plus other websites that are significant to you – and different with that hologram-bank, there’re resolutions to this. First of all, you will require running good antivirus software on your mobile, desktop, laptop or tablet so that robbers cannot attack your device with malware. In addition, you should look after the “invalid certificate” messages on your websites with some HTTPS domain names. One of those messages can appear any time, and you might be being indicating to a duplicate and should drop out of there ASAP.
Another option is prefer using a third-party Domain name system server. Your ISP (internet service provider) has a by default DNS server, however that does not imply that you need to employ it. For instance, Tenta provides access to a number of DNS, containing our individual Tenta-DNS, plus a variety of other famous 3rd party DNS servers. When you get linked through a nice 3rd party DNS, you will typically have further protection and security than if you link through your default ISP-server. The reason is as several 3rd party DNS servers have state-of-the-art security measures that are not still applied on the default ones. We have spent a lot of time on the internet and do loads of our own business on the web – today it just makes sense to secure yourself. Now you are aware of the DNS servers and you also know how they can assist you, you have take one-step ahead towards ignoring the duplicates.
Interesting facts about Domain Name System
Here are some interesting facts about DNS you should be aware of –
-
The History of DNS
Today’s users should be aware of the development of DNS. DNS system basically is over 30 years old. This theory was primarily used to assist with rising email contacts on the ARPANET. Domain Name System was created by one of the creators namely Paul Mockapetris. Before the arrival of DNS, a public-system could exclusively be recognized by its hostname. The addresses attached to each and every hostname are kept in a big file (named hosts.txt). This was the system which was very hard to hand le following the development of computer networks in the years 1970s and 1980s. Domain-name system was the extension of this single-level identification system to the multi-level system, via the accumulation of support domains. This simply implies that one or multiple names were added to the hostname, along with a dot dividing each extra name.
-
DNS Structure
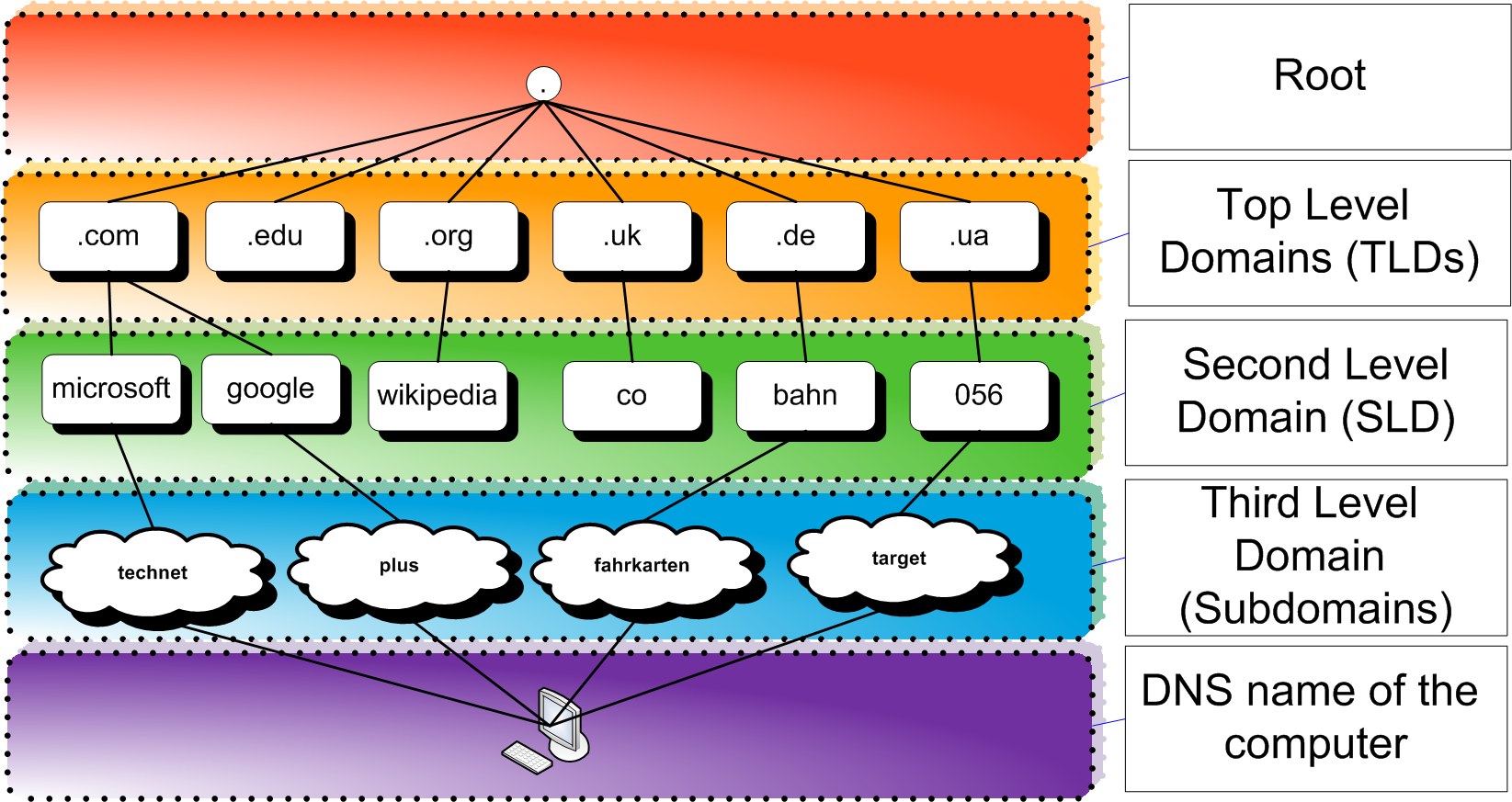
It is depending on a hierarchical shared database regulated by different protocols. The DNS names form a hierarchical structure which is said to be the domain namespace. These names are connected to personal labels, which are divided by . (dots). Any domain-name that is completely qualified will be distinctive enough to be certain by the position of the host on the DNS-tree. Frequently a DNS database is separated into various sectors. Every sector accepts a part of the DNS-database. They accommodate the source records of the domain names that include the namespace. Per se, every sector is part of a specific domain, which is known as its root. A sector includes all the information about the domain names and finishes in the root-name of the domain. There are some typical categories that are used to explain domain names plus their roles:
- Top level domains (.TDLs): These are employed to represent a nation, region, or an organization.
- Root domains: These are located at the peak level of DNS tree, and they describe a nameless level. They indicate a precise location on the DNS hierarchy.
- 2nd level domains: These domains are usually variable length domain names that are allotted to suitable TDLs based on the organization or geographical location.
- subdomains/ 3rd level domains: They are employed to represent organizations made from the 2nd level domains. These consist of the terms that are included to boost the hierarchical organization.
-
Functions of DNS
The DNS is basically a database which is tasked with keeping the website names and connecting them to IP-addresses including a numerical pattern. Also DNS aids to find the IP addresses to particular site names and then saves this information. This procedure is called as record-maintenance. Its role is to share the DNS over a huge network-of-connections. Also this system can have a huge collection of records. DNS database can effortlessly be distributed because each server has a small section of IP-address together with hostname mapping information.
The records of IP-address to mapping of hostname is said to be the namespace. At what time a user sees a domain name in the DNS, and then they should check the advanced database which redirects the consumers on how you can verify the DNS server-host. Then system identifies queries that can easily be resolved by the client through the host-name given by the DNS-server. This procedure keeps until the user finds the right web server hosting the needed DNS. The report kept by the domain-name system can be helpful for other services plus can help apps. DNS may look like intricate, however just as other processes like email depends on it to work.
-
DNS-Leaks are Common
Usually a DNS-leaks means a case where the IP address of a user becomes noticeable to the public-domain following they’ve taken some major steps for hiding the IP. Today, several internet users use various methods to conceal their IP-addresses from their respective ISPs and potentially nasty people on the web. The majority of such tools are handled by channeling web traffic over a huge computer networks. At what time the traffic do not succeed to redirect through secured channel and go through the ISP, then DNS leaks takes place. Luckily, you can prevent this situation by following a comprehensive guide.
-
DNS-Hijacking is Possible
News of DNS hijacking keeps coming every now and then. DNS hijacking is a virtual assail in which the hacker becomes capable to get access to DNS information of a target site. Then the hacker moves on to change this information to redirect the visitors of the website to another website controlled by them. When a web user goes to a website that has been hijacked by a hacker, the DNS consults to the browser to ask for information from the fake website of hacker. It is important to note that hijacking don’t have to negotiate the DNS itself for doing such virtual attacks. They just need to negotiate the service which is hosting the domain. The regularly do this by acting as web administrators. DNS-hijacking can be especially hard to protect against.
-
Works in Reverse and Forward
A huge ratio of requests to the domain-name-system targets to convert the website hostname and web-server to the IP-addresses. These are known as forward DNS mapping or lookups. Also, DNS works in the reverse track. The DNS can convert IP-addresses to hostnames. This kind of request is called as reverse DNS mapping or lookups. Reverse DNS lookups or mapping are said to be very common. But, they cater as an extremely helpful job for network admin because they aid with the process of troubleshooting. A mail-server can also use reverse lookups to perform sanity checks following another mail-server attached to it. The IP-address segments are reversed at the time of reverse mapping.
-
DNS has developed to 700 TLDs
At present, internet accommodated over 700 TLDs (top-level domains). TLDs basically refer to a single domain on the top–level of hierarchical DNS of the web. It is the ultimate label of a completely qualified domain-name. A few of these TLDs hold some odd names like .rocks and .soy. The distribution of TLDs is managed by the ICANN (Internet-Corporation-for-Assigned Names-and-Numbers) which is a nonprofit leading organization. Bur, only 6 TLDs were described by DNS when it was initially applied again in the 1980s. These comprised .mil, .org, .net, .edu, .gov, and .com. In the year of 2011, there was a wonderful development in TLD options. This catered to categorize sites as per their intentions for ease.
Conclusion
DNS gets presumed mainly as it’s not something that user face frequently at the time of using the net. This is the reason behind the existence of the internet for over 2 decades.